
Simm.BI is an innovative and revolutionary system that provides BI solutions - a complementary product for information systems in small and medium businesses. Simm.BI allows for the first time the use of advanced BI tools, which until now only only giant corporations could afford.
This innovative tool is SaaS software that sits in the cloud and does not require physical installation on the company's server. The software automatically learns the structure of the SQL database of each information system used by the company, being the first BI solution in the world that requires minimal integration.
After a simple process of a few hours in which the BAI Technologies team learns about the company's activities and needs, the initial connection requires only a few minutes, and the system can be started immediately.

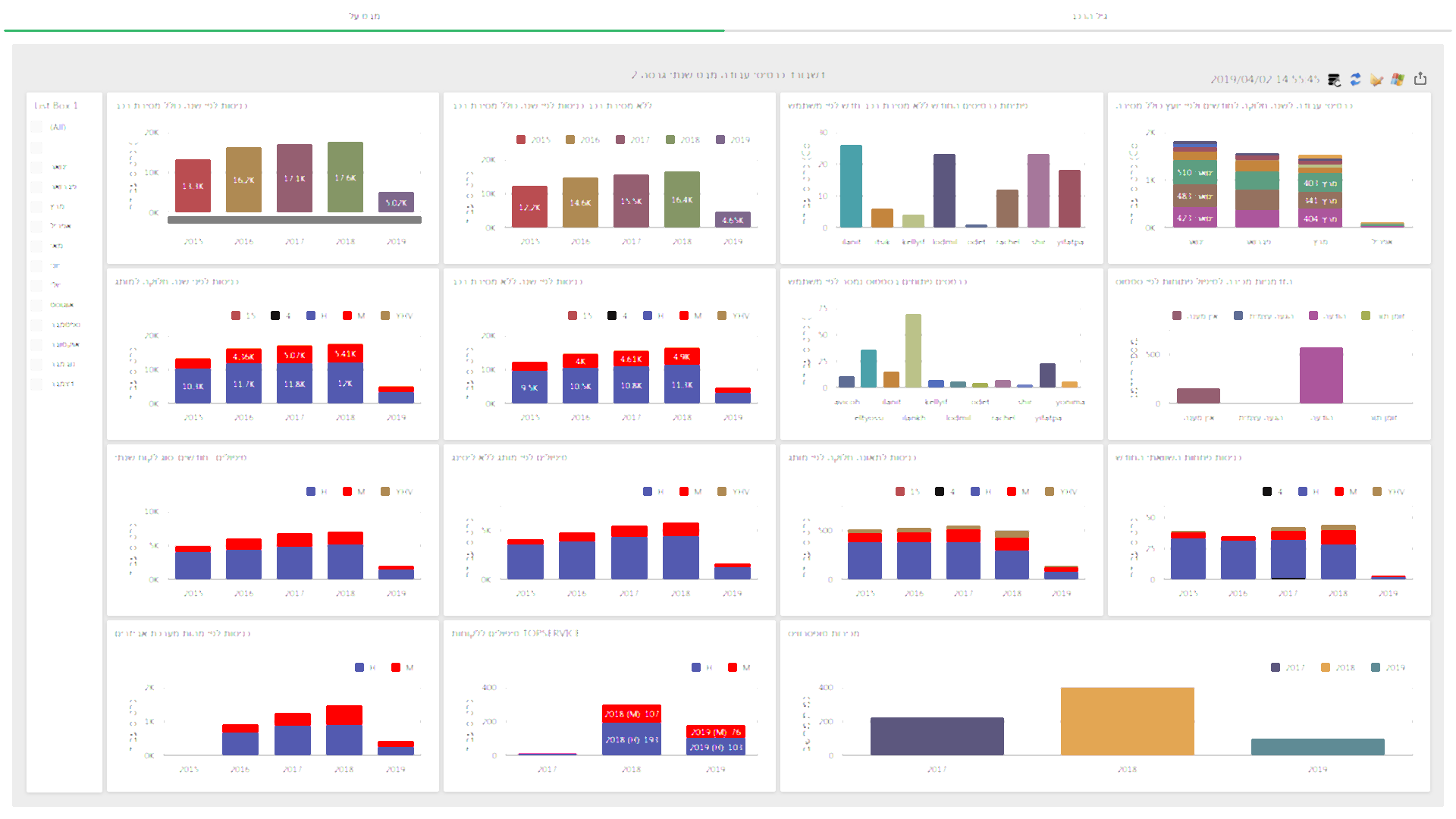
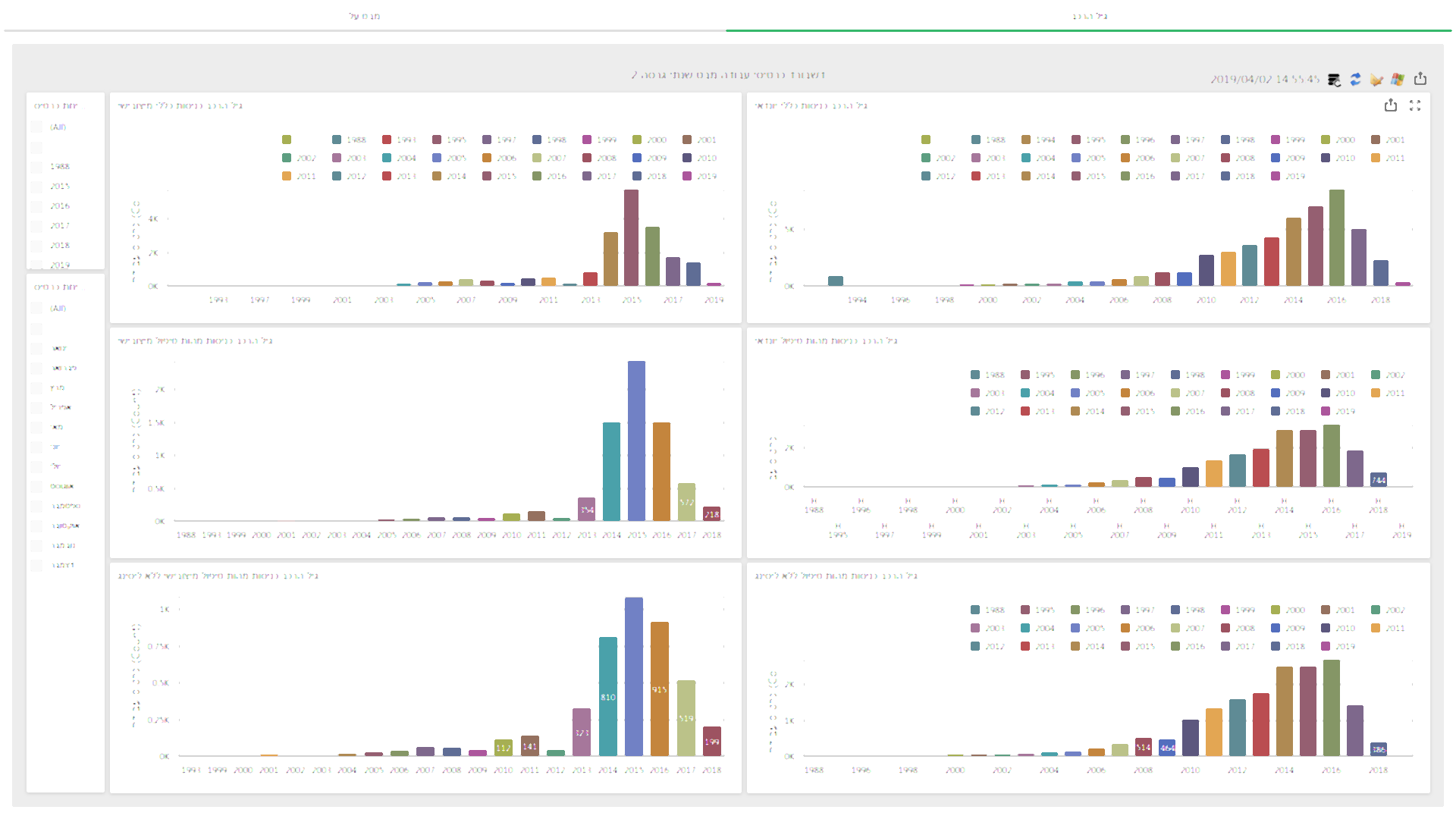
Simm.BI is the only system in the world that can learn any database without human contact, enabling managers and employees to create reports of any kind, format reports, consolidate existing reports and build dashboards easily and in real time. This means that for a nominal cost, each organization can utilize the information stored in the information systems and make quality decisions on a daily basis in a simple, accessible and fast process.
With Simm.BI, you can build reports that combine data from each module and every area of the information system, even integrating data from multiple information systems, all via a simple interface for each user that improves the decision making process in the organization.
Building a new report is a simple process where you define a report by selecting the fields you want from the information system, defining properties
such as input, adding computational columns or functions, then saving the report.
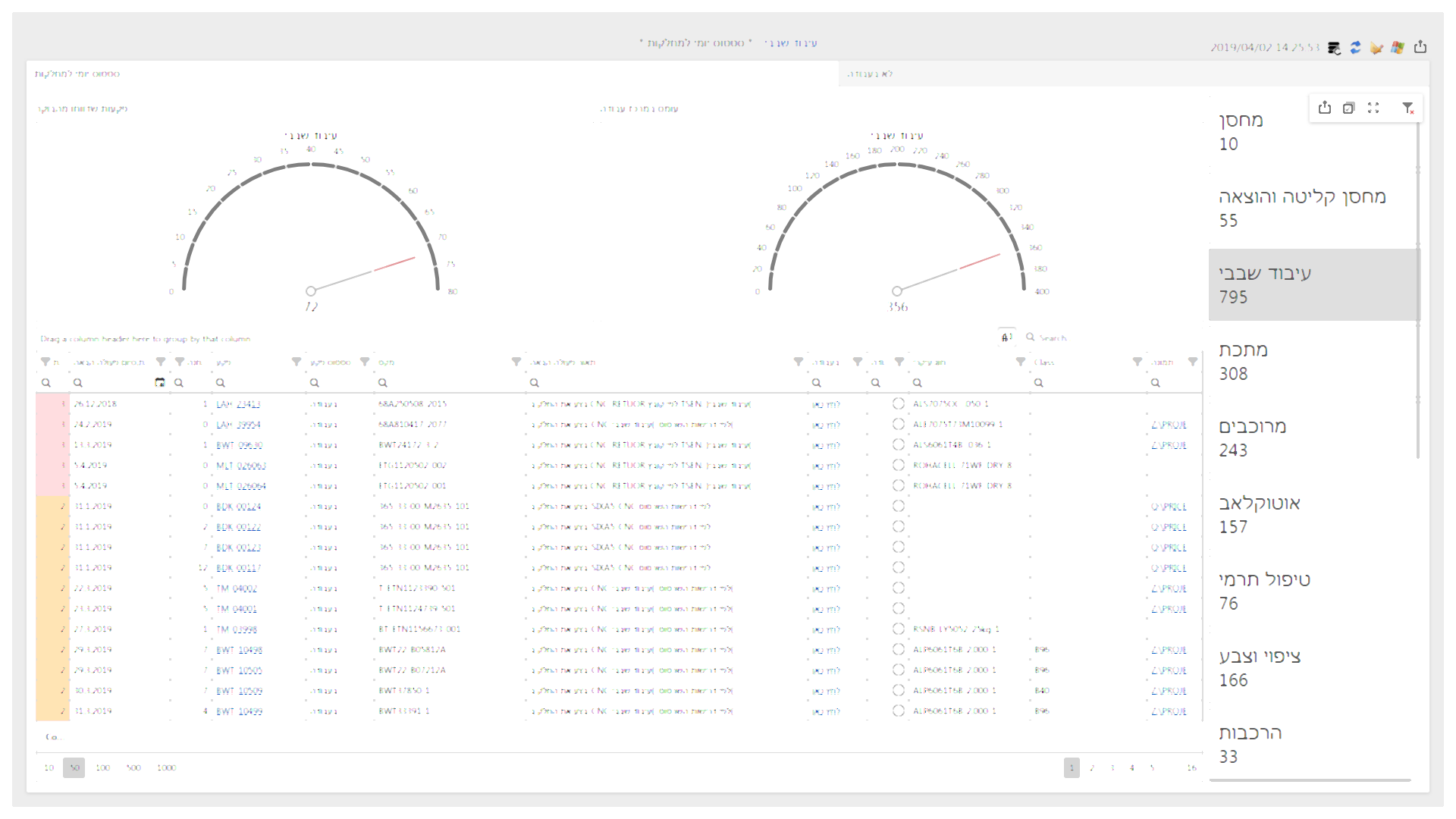
In this screen, you can change any setting set in the report building stage, format the defaults when generating the report, add or download fields, and satisfy any requirement that arises when using the report.
Reports are easy to find: you can search for the report by a free text search, from any folder or from the list of reports in the system. Once the report has been generated, the user has a very wide range of convenient tools to analyze the data from different angles by adding, cross-referencing or removing data then displaying them in different ways.
The Simm.BI system is stored on a server farm with extremely heavy security (physical and technological). The budget required to break into such a system is more on the level of countries, not companies.
As a result, the only reasonable danger to the organization’s data comes from hacking into the organization’s computers, which are usually not secured by Simm.BI.
For safety, six different layers are used to secure the information, listed below.
One-way flow – The Simm.BI system does not have access to the organization’s internal server.
In the process of building or producing a report, the Simm.BI system does not address the organizational server.
When the end-user selects the fields that he wants and requests the report, he leaves a request on the Simm.BI server; the internal database of the organization samples the system 4 times a second, and when it detects a request, initiates an authentication process initiated by the request, then sends the specific data of the requested report to the end user.
The information is not saved in the cloud but on your computer
Only the database structure of the organization’s internal database is stored in the Simm.BI system, not the actual data. When the database identifies an end-user request and sends the requested report data, the information is passed and saved to the end user’s computer rather than in the cloud.
Thus once the report has been generated, you can edit, format, modify, or save it without the need for an Internet connection because the information is stored on your computer.
Cloud security (server farm)
The Simm.BI system, which is stored at Bezeq International’s server farm, benefits from data security based on collaborative FW (the Fortigate 5131 solution, which is the Cluster NBF firewall), as well as physical security 24/7.
Cloud security (server farm)
The Simm.BI system, which is stored at Bezeq International’s server farm, benefits from data security based on collaborative FW (the Fortigate 5131 solution, which is the Cluste NBF firewall).
As well as physical security 24/7.
Protocol 443 (https)
The use of this protocol secures the data traffic that passes through the network. This protocol is used by the most secure sites in the world such as banks, PayPal and etc.
Protocol 443 is essentially coding and encrypting HTML content based on ssl / tsl protocols and enabling client-server communication securely using technologies such as asymmetric cryptography for key exchange, symmetric encryption of information confidentiality and message-approved codes to authenticate parties.
A mechanism to identify users by specific location or device.
The Simm.BI system allows the database to define the identity of the specific computers that are authorized to receive data so that the organization can restrict the sending of data to the IP of the enterprise modem only or even assign IP to specific mobile phones or laptops and thus not allow access from any computer, A valid username and password are also required.
Secure external mechanism for user identification.
Simm.BI uses an innovative method for verifying user identity: your database receives a key table (in the list of “questions” where each question has only one correct answer). Another copy of the table is stored in a privileged place which BI can access.
In the unlikely event that a click-BI system is hacked, the intruder can leave a message to the organization’s internal server requesting data, but without the verification table, the hacker’s identity cannot be verified and so the database will not send the requested information.
Due to this method, it is necessary to break into the organizational server in order to access the data . But should this happen, there is no need to access the Simm.BI system because the data is stored on the same server.
The information security system, whose principles are detailed on this page, is backed by the strict procedures of Simm BI Technologies Ltd., undergoing extensive weekly reviews and tests.